Rockwell Automation SLC 500 Series Programmable Logic Controller
Rockwell Automation SLC 500 Series Programmable Logic Controller
Introduction: The classic cornerstone of industrial automation
In the field of industrial automation, the Allen Bradley SLC 500 series programmable logic controller (PLC) occupies an indelible historical position. As a key bridge connecting early relay control systems with modern complex networked control, SLC 500 not only demonstrates extremely high reliability in hardware, but its instruction set system also lays the foundation for programming concepts on subsequent platforms such as ControlLogix. This article is based on the 1747-RM001G-EN-P reference manual and aims to provide an in-depth analysis of the core instruction system of SLC 500, from the underlying data architecture to advanced closed-loop control, providing automation engineers with a highly practical and valuable professional guide.
Chapter 1: The underlying logic of processor file architecture
To master SLC 500 programming, the primary task is to understand its memory architecture. The user memory of SLC 500 is strictly divided into two categories: data files and program files. This structured design ensures efficient addressing and secure isolation of data.
1. Fine division of data files
The data file numbers range from 0 to 255, and the system assigns specific file types by default:
I/O Image Area (File 0&1): File 0 is the output image, and File 1 is the input image. Its addressing format strictly follows the structure of O: e.s/b or I: e.s/b. Among them, e represents the physical slot number, s represents the word address (for modules with more than 16 I/O points), and b represents the bit number. This method of directly binding physical location with logical address greatly facilitates on-site wiring verification.
Status file (File 2, S:): This is the "black box" of the processor, which records key information such as system clock, error codes, communication status, etc. For example, S: 1/15 is the first scan bit, commonly used for system initialization; S: 5/0 is a math overflow trap bit, if not reset in time, it will cause the processor to crash.
Data storage area (File 3-8): The default configuration includes bit files (B3), timers (T4), counters (C5), controls (R6), integers (N7), and floating-point numbers (F8). It is particularly noteworthy that the timer and counter are a 3-bit element structure, containing control words, preset values (PRE), and cumulative values (ACC), respectively. This composite structure requires special attention to the difference between word addressing and bit addressing during programming.
2. Hierarchical management of program files
File 2 is the main program, and files 3 to 255 are subroutines. Through this division, engineers can decouple complex process logic into independent modules, enabling code reuse and maintenance.
Chapter 2: Fine Control Mechanism of Basic Instructions
The basic instructions form the backbone of ladder logic, but in SLC 500, seemingly simple instructions hide strict timing and state preservation mechanisms.
1. The combination of virtual and real logic
XIC (check for closure) and XIO (check for disconnection) are not simply reading physical states, but checking for "logic 1" or "logic 0" in the data table. This means that if a physically disconnected button (input 0) is latched (OTL) to 1 in the program, the XIC instruction will still be judged as true. OTE (Output Excitation) is non hold type, and its state will be reset if it is in the MCR (Main Control Reset) disabled area or power off; OTL (latch) and OTU (unlock) have retention characteristics, which require extreme caution in safety circuit design.
2. Three forms of timers
TON (Connection Delay): The most commonly used timer that starts counting when the step condition is true, and when the preset value is reached, the Done bit (DN) is placed. When the condition becomes false, it is immediately reset.
TOF (disconnection delay): Timing starts when the step conditions become false. Engineering Pit Avoidance Guide: Never use RES (Reset) command to reset TOF, as RES will clear all status bits, causing timing confusion.
RTO (Hold Timer): Even if the step conditions become false or power is lost (with battery backup), the accumulated value will be maintained. It must be manually reset through the RES command, which is commonly used to record the accumulated running time of the device.
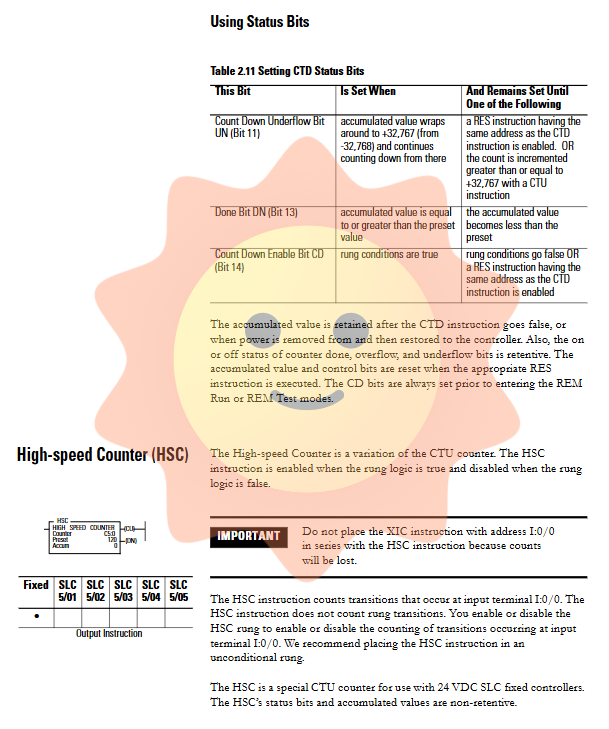
3. Counter and high-speed pulse processing
CTU (up counting) and CTD (down counting) are triggered along the transition edge from false to true in the cascade. When the count value exceeds+32767, the overflow bit (OV) is set and the value becomes -32768, which is a characteristic of signed integer complement. For the fixed SLC 500, the HSC (high-speed counter) instruction allows direct processing of hardware pulses up to 8kHz, but this requires physically disconnecting the J2 jumper inside the controller, configuring I: 0/0 as high-speed input mode, and asynchronous delay between its software accumulation value and hardware count value.
Chapter 3: Advanced Applications of Data Operations and Comparisons
In modern control systems, simple traffic light logic is no longer sufficient, and data processing and computation have become the core.
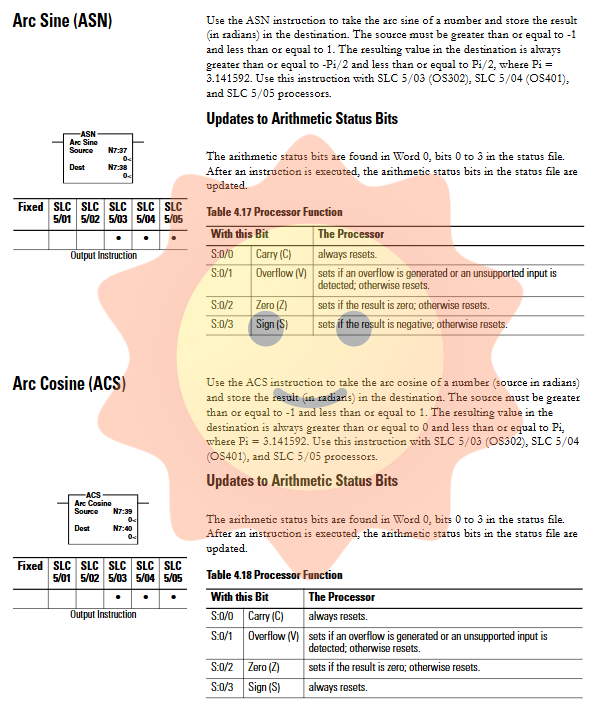
1. Game between mathematical instructions and state bits
When executing instructions such as ADD, SUB, MUL, DIV, etc., the processor updates the arithmetic state file (S: 0). Among them, the handling of overflow bits (S: 0/1, i.e. V bits) is a major disaster area in programming. If the result of the operation exceeds the range of 16 signed integers (-32768 to 32767), the V position is taken. If S: 5/0 (minor error bit) is still 1 at the end of the scanning cycle, the processor will report an error and shut down. Therefore, the professional programming habit is to immediately use OTU instructions to reset S: 5/0 after mathematical operations, or use S: 2/14 (mathematical overflow selection bit) to implement truncation processing for 32-bit addition and subtraction operations.
2. Block transfer and data scaling
In analog processing, SCP (with parameter scaling) instruction is a powerful tool. It directly maps the raw ADC values from 0-32767 to engineering units (such as 0-100.0 PSI) based on the linear equation y=mx+b operation. In contrast, the SCL (data scaling) instruction uses the form of Rate/10000, which has a complex calculation process and is prone to overflow in intermediate steps. SCP is more recommended in modern programming.
3. Logical traps in comparing instructions
The LIM (Limit Test) instruction has a unique inversion logic: when the low limit is greater than the high limit (such as low limit=10, high limit=5), the instruction outputs false when the test value is between 5 and 10, and true when it is less than 5 or greater than 10. Although this design is clever, it is easily overlooked during code review, leading to logical errors.
Chapter 4: Black Technologies for File Operations and Stack Management
SLC 500 provides efficient file instructions for processing large amounts of data.
1. In depth analysis of COP and FLL
COP (File Copy) and FLL (File Fill) are powerful tools for handling arrays. The key lies in the explanation of the "length" parameter: it is measured in units of the elements of the target file. For example, copying an integer file (1 word/element) to a timer file (3 words/element), if the length is set to 10, the actual copied data amount is 30 words. This mechanism is very practical in data type conversion, but it is also prone to causing memory out of bounds errors.
2. Asynchronous coordination between FIFO and LIFO
FIFO (First In First Out) and LIFO (Last In First Out) instructions manage the stack through the control element (R6). FFL (load) writes data at the position pointer and increments the pointer, while FFU (unload) reads data from position 0 and moves the entire array forward. In a multitasking environment, it is necessary to ensure strict timing matching between loading and unloading, otherwise it may lead to data misalignment. The DN (full) and EM (empty) bits in the control word are key monitoring points for achieving production cycle synchronization.
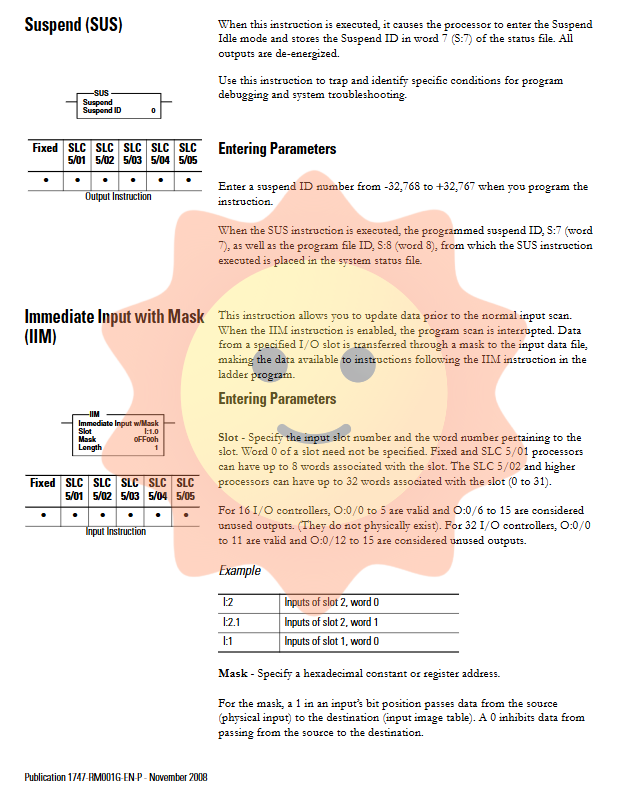
Chapter 5: Program Flow Control and System Architecture Optimization
A good program architecture is not only related to execution efficiency, but also to the maintainability of the system.
1. Nested risk of subroutine calls
JSR (jump subroutine) allows up to 8 levels of nesting (only 3 levels are allowed within interrupt subroutines such as STI or DII). Although nesting can save code, excessive nesting can lead to stack overflow risks. More importantly, if the output coil (OTE) is located in a subroutine, the output will maintain its final state between two calls, and this "implicit memory" is often the culprit of on-site faults.
2. Boundary trap of MCR (Master Reset)
MCR is used to isolate equipment maintenance areas or formula switching areas. However, it is strictly prohibited to jump (JMP) into the MCR area. Because once jumped in, the processor may misjudge the state of the MCR starting step, which may cause accidental excitation of the output that should have been isolated, resulting in serious safety accidents. In addition, MCR is not a hardware power outage, and the behavior of the timer in the MCR disabled area (such as TOF continuing to count) is different from physical power outage.
3. Precise Strike of Interruption Mechanism
For SLC 5/03 and above processors, STI (optional timed interrupt) and DII (discrete input interrupt) allow breaking the constraints of sequential scanning. Putting PID operations or high-speed encoder readings into STI subroutines can ensure absolute constant control cycles. However, it should be noted that interrupt service programs (ISR) should be as short as possible to avoid blocking the main logic.
Chapter 6: Practical Application of Special Instructions in Complex Processes
1. Shift Register (BSR/BSR)
In assembly line tracking, the BSL instruction is preferred. It shifts the entire bit array to the left, with new data entering from the Source bit and overflow bits entering the UL (unload) bit. By monitoring the UL position, the moment when the product reaches a specific workstation can be accurately captured without the need to write lengthy state machine code.
2. Sequencer (SQO/SQC)
SQO (Sequential Output) traverses pre-set data files through step pointers and outputs different bit patterns to physical ports using masks. This is more intuitive than complex ladder diagram interlocking logic. SQC (Sequential Comparison) is commonly used for step confirmation, which compares the input state with the reference mask and uses the FD (Find) bit to determine whether the current step is completed.
3. Bottom layer handshake for block transfer (BTR/BTW)
When communicating with special I/O modules such as servo drives and smart meters, BTR/BTW is the only bridge. It asynchronously exchanges data with scanners (such as 1747-SN) through M0/M1 files as buffers. The handshake timing in the control block is extremely strict: EN (enable) is set by the program, ST (start) and DN (finish) are set by the hardware scanner, and the program must immediately clear EN after detecting DN, otherwise the next transmission will be blocked.
Chapter 7: The Art of PID Closed Loop Control
The PID instruction is the most complex monolithic instruction in SLC 500, with its 23 word control block hiding a lot of control details.
1. Independent integer algorithm
Unlike PLC-5 or ControlLogix which use floating-point PID, the PID of SLC 500 is completely integer operated, and the internal variable range is forcibly limited to 0-16383. This means that all analog inputs (such as 3277-16384 corresponding to 4-20mA) must first be scaled to this range through SCL or SCP commands.
2. Anti integral saturation and hand automatic undisturbed switching
When the output is limited, if no measures are taken, the integral term will accumulate infinitely, resulting in the output still being unable to fall back after the deviation is eliminated (i.e. integral saturation). The SLC 500 achieves hardware level anti saturation through OL (output limiting enable) and CL bits. At the same time, in manual mode (AM=1), the algorithm will automatically adjust the integral sum to ensure that when switching back from manual to automatic, the control variable (CV) will not undergo step jumps, achieving true disturbance free switching.
3. Selection of Timing Mode and STI Mode
Although PID supports internal scheduled updates, this mode is not recommended in circuits with strict requirements due to the jitter of the scanning cycle. The best practice is to place the PID into an STI subroutine that strictly matches the cycle with the 'Loop Update' parameter to obtain a deterministic control cycle.
Chapter 8: Fault Diagnosis and System Robustness Design
1. Deep mining of status files
S: The six characters contain the code for the last major malfunction. For example, error code 0020 usually points to an unprocessed mathematical overflow; Error code 0036 indicates that the PID parameter is out of bounds. By using the user fault subroutine (file 3 or specified file), it is possible to record the fault context before the processor crashes, and even attempt a soft reset for non fatal errors.
2. Communication diagnosis of I/O module
For remote I/O (RIO) networks, use G files (dedicated I/O module data) to monitor the module's network access and disconnection status. For local expansion racks, the disconnection situation is determined by checking the specific position of the input image (if supported by the module), rather than relying on simple cascade logic.
3. Defense design for power failure
Although SLC 500 has power failure protection function, the worst-case scenario should be assumed during design. Use S: 1/15 (first scan position) to forcibly initialize key control positions (such as hydraulic start permission position, safety door status) during each power on, to avoid dangerous actions after restart due to data flipping at the moment of power failure.
- ABB
- General Electric
- EMERSON
- Honeywell
- HIMA
- ALSTOM
- Rolls-Royce
- MOTOROLA
- Rockwell
- Siemens
- Woodward
- YOKOGAWA
- FOXBORO
- KOLLMORGEN
- MOOG
- KB
- YAMAHA
- BENDER
- TEKTRONIX
- Westinghouse
- AMAT
- AB
- XYCOM
- Yaskawa
- B&R
- Schneider
- Kongsberg
- NI
- WATLOW
- ProSoft
- SEW
- ADVANCED
- Reliance
- TRICONEX
- METSO
- MAN
- Advantest
- STUDER
- KONGSBERG
- DANAHER MOTION
- Bently
- Galil
- EATON
- MOLEX
- DEIF
- B&W
- ZYGO
- Aerotech
- DANFOSS
- Beijer
- Moxa
- Rexroth
- Johnson
- WAGO
- TOSHIBA
- BMCM
- SMC
- HITACHI
- HIRSCHMANN
- Application field
- XP POWER
- CTI
- TRICON
- STOBER
- Thinklogical
- Horner Automation
- Meggitt
- Fanuc
- Baldor
- SHINKAWA
- Other Brands
- UniOP
- KUKA
- Iba






































































































































