OMRON NJ/NX OPC UA Configuration Guide
OMRON NJ/NX Series Controller OPC UA Server Implementation and Security Configuration Complete Guide
In modern industrial automation systems, breaking down the data barriers between the control layer and IT systems (such as MES, SCADA) is the key to achieving intelligent manufacturing. OPC UA (Open Platform Communication Unified Architecture), as a platform independent, secure and reliable communication protocol, has become the core standard of Industry 4.0. Omron has integrated OPC UA server functionality into its NJ/NX series Machine Automation Controller, allowing the upper system to directly and securely access variable data within the controller through standard Ethernet without the need for intermediate conversion computers. This article aims to provide engineers with a detailed technical guide on configuring, optimizing, and maintaining OPC UA servers on NJ/NX series controllers.
System Overview and Applicable Hardware
The OPC UA server function enables NJ/NX series CPU units to act as OPC UA servers, accepting connection requests from SCADA or other OPC UA clients, and enabling read and write operations on global variables and function block instances within the controller. This feature is deeply integrated with the built-in EtherNet/IP port (specific port) of the controller.
Supported CPU models:
Not all CPUs support this feature, please confirm the hardware version before use:
NX701-1 □□□: Unit version 1.24 or higher.
NX502-1 □□□: Unit version 1.60 or higher.
NJ501-1 □□□: Unit version 1.17 or higher.
NX102- □□□□: Unit version 1.30 or higher.
Key specification limitations:
Connection port: limited to the built-in EtherNet/IP port of the CPU unit (specifically PORT 1 for NX701/NX502/NX102).
Maximum number of sessions: The server can support up to 5 OPC UA client sessions simultaneously.
Monitoring items: The entire server supports up to 2000 monitoring items (up to 20000 for specific models and higher versions).
Number of variables to be published: Up to 10000 network variables can be published (the higher version NX701 supports 100000).
Detailed configuration steps: from beginner to proficient
The configuration of the NJ/NX OPC UA server is mainly divided into four stages: network layer settings, security settings, variable publishing, and online operations, all of which are carried out in Omron's Sysmac Studio software environment.
2.1 Basic Network Settings: Determination of IP Address
OPC UA communication relies on a stable IP address.
Navigate to Configuration and Settings ->Controller Settings ->Built in EtherNet/IP Port Settings.
In TCP/IP settings, select "Fixed settings" or "IP address obtained from BOOTP server".
Important warning: It is strongly not recommended to use DHCP (Dynamic Host Configuration Protocol). The server certificate is bound based on the IP address at the time of generation. If there is a subsequent change in IP address, it will result in a mismatch between the server certificate and IP, causing client connection failure and triggering the 'Server Certificate Mismatch' event.
2.2 OPC UA Server Core Settings
Enable service:
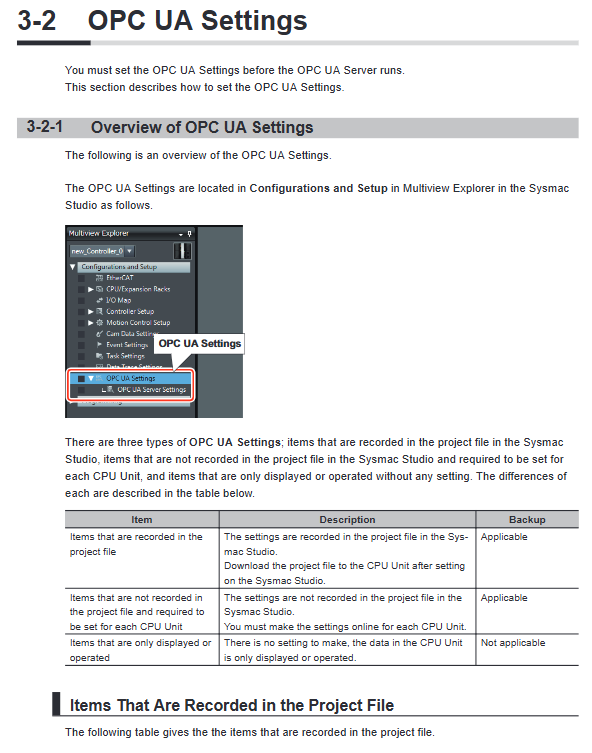
In the multi view browser of Sysmac Studio, find Configuration and Settings ->OPC UA Settings ->OPC UA Server Settings.
Change the 'Server Function Settings' from' Do Not Use 'to' Use '.
Key step: After downloading this project to the controller, it is necessary to cycle the controller to power off and then power on or perform a "controller reset" before the OPC UA server can start.
Endpoint and Port Configuration:
The 'Endpoint' field will automatically display the server's URL in the format of opc.tcp://[IP address]: [port number]/. The default IP is 192.168.250.1 and the default port is 4840.
The 'port number' can be customized (range 1025 to 65535), but it is necessary to ensure that the port is not occupied by other services such as FTP, HTTP, etc.
Execution log settings:
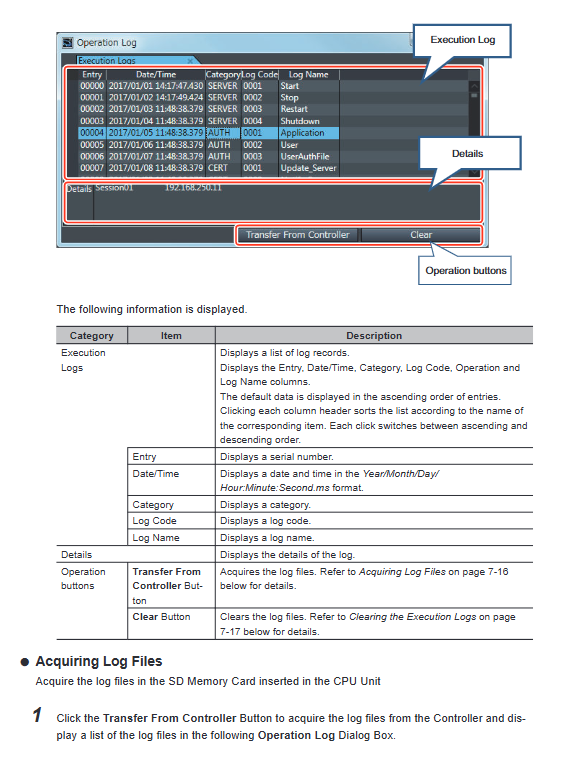
To trace the operational status, connection requests, and errors of OPC UA servers, it is strongly recommended to enable execution logs.
Set 'Record Execution Log' to 'Record'.
The number of configurable files (2-100) and the number of records per file (100 to 65536). The log files are saved on the SD memory card of the CPU unit.
2.3 Variable Release: Building Address Space
OPC UA clients need to access controller data through address space. Engineers need to specify which variables are visible to the outside world.
Global variable release:
In the global variable editor, find the variable that needs to be published.
Set its' Network Publishing 'attribute to' Publish Only ',' Input ', or' Output '. System defined variables cannot be published.
User defined feature block variable release (supported in higher versions):
You can select a specific namespace or feature block instance for publishing in the "Network Publishing Settings" of the "OPC UA Server Settings".
This allows structured control logic (such as motor control blocks) to be directly exposed to the upper system.
Expansion control of structures and arrays:
In the 'Node Settings', you can control whether to' expand structure members' and 'expand array elements'.
When selecting 'expand', each member of the structure or each element of the array will be published as an independent node, making it easier for the client to read and write finely. Choosing 'not expand' will treat the entire node as a whole, with a smaller communication load.
Deep Analysis of Security Models
The core advantage of OPC UA lies in its security. The NJ/NX controller implements multiple layers of security mechanisms to ensure that only authorized clients and users can access data.
3.1 Application authentication: Handshake based on X.509 certificate
This is authentication between the server and the client.
Server certificate:
The CPU unit serves as a server and holds a self signed certificate.
Automatic generation: After setting OPC UA to "use" for the first time and restarting, the system automatically generates a certificate using the IP address of the current built-in EtherNet/IP port. Its validity period is usually 20 years.
Manual regeneration: When a 'server certificate mismatch' or IP address change occurs, the certificate must be manually regenerated. Operation path: In online mode, right-click on OPC UA server settings ->server certificate ->regenerate certificate. DN information (organization, city, country, etc.) and validity period can be modified here.
Export: After generating a new certificate, it must be saved as a. der file using the "Export" button and installed on all OPC UA clients that allow connections.
Client certificate:
The client needs to prove its identity to the server.
Import: Administrators can add trusted client certificates (. der files) to the "Trusted Certificate List" of the controller.
Auto Reject: If an unregistered client attempts to connect, its certificate will be automatically placed in the "Reject Certificate List" and the connection will be rejected. The administrator can move the certificate from this list to the trusted list in the future to authorize the client.
3.2 User authentication: Control operation permissions
In addition to device authentication, operator authentication can also be performed.
Username/Password: Administrators can add up to 20 users in "Security Settings". Username (4-32 characters) and password (8-32 characters) are case sensitive.
Anonymous login: You can choose "disable" or "allow". For security reasons, it is recommended to prohibit anonymous login in actual production environments.
Role function (supported in higher versions):
Different users can be assigned roles (Observer, Operator, Maintainer, Designer, Administrator).
The hierarchical progression of role permissions. For example, Observer can only browse and read, not write; And Operator and above can execute methods and write variables.
Even the required roles can be set for different namespace nodes to achieve fine-grained permission control.
3.3 Message Security Strategy: Encryption and Signature
In the "Security Policy" section of the "Security Settings", you can define the communication encryption modes allowed by the server.
None: Not recommended for use in production environments.
Signature: Only sign the message to ensure data integrity (tamper proof), without encryption.
Signature and Encryption: Simultaneously sign and encrypt the message to ensure integrity and confidentiality (anti eavesdropping).
Algorithm selection: Supports Basic128Rsa15, Basic256, Basic256Sha256, as well as newer Aes128Sha256RsaOaep and Aes256Sha256RsaPss.
Best practice: For security reasons, clear the "none" and weaker Basic128Rsa15 options, and choose "sign and encrypt" combined with strong algorithms.
Client Connection and Data Interaction
After completing the server-side configuration, the OPC UA client can connect.
Connection URL: The client needs to use the URL defined in the "endpoint" for connection, such as OPC tcp://192.168.250.1:4840/ .
Security negotiation: The client must choose the security policies and modes allowed by the server.
User login: Depending on the server settings, provide a username/password or perform anonymous login.
Address space browsing: After a successful connection, the client can browse the address space. The typical structure is Objects ->DeviceSet ->[Controller Name] ->GlobalVars, where all published variables can be seen.
Read and write operations: The client can read or write to specific nodes. Write permission is subject to a combination of variable attributes (such as constants), user roles, and node security policies.
Operation, maintenance, and troubleshooting
5.1 Start and Stop
Startup: As mentioned earlier, it automatically starts after downloading the configuration and restarting the controller.
Manual stop: You can execute the OPCUA_Shutdown command or click "Server Shutdown" on the "Server Status" page of Sysmac Studio. After stopping, the controller needs to be restarted before it can run again.
5.2 Status Monitoring
Server Status: When Sysmac Studio is online, check the "Server Status" page to obtain the current status (running, error, closed), the number of connected clients, and the number of users.
Event log: The controller's event log will record OPC UA related errors (such as certificate mismatch, variable count exceeding limit, etc.).
Execution log: A detailed log file stored in the SD card, which records authentication success/failure, variable access details, etc. You can view it through the "Display Operation Log" window of Sysmac Studio or directly on the SD card (file path:/packages/OPCUA_Server/ExecutionLog/).
5.3 Common Errors and Countermeasures
Server certificate mismatch (event code 15020000 hex):
Reason: The IP address of the controller has changed, but the server certificate has not been regenerated.
Solution: Manually regenerate the server certificate and export the new certificate for installation on all clients.
Connection rejected (client in rejection list):
Reason: The client's certificate was not added to the controller's' trusted certificate list '.
Solution: On the client authentication page, move the corresponding certificate from the "Rejected Certificate List" to the "Trusted Certificate List".
Variable cannot be read or written:
Reason: Variable size exceeds 60KB; array starting index is non-zero; Structure nested more than 3 layers; The total number of global variables exceeds the upper limit; Insufficient user role permissions.
Check: Check the execution log for records related to SERVER-0100 or SERVER-0101, and adjust the variable structure or optimize the number of publications according to the prompts.
5.4 Hardware replacement and backup recovery
CPU replacement: Server certificates are hardware related information and are not included in regular backups. After replacing the CPU, even if the backup is imported, the server certificate must be regenerated on the new CPU and the new certificate must be exported and installed on the client.
Backup strategy: The controller backup function of Sysmac Studio can backup OPC UA server settings, client certificates, security policies, etc. But when restoring, you can choose whether to restore the OPC UA security configuration file. Execution logs need to be managed separately as they are stored on an SD card.
Performance considerations and system design
Startup time: The startup time of the OPC UA server (from restart to running state) is related to the number of variables published and the proportion of task execution time. The more variables there are, the slower the startup.
System service execution time: The OPC UA server runs as a system service. If the CPU task cycle is too full, resulting in insufficient system service execution time (reference value below 20%), it will cause OPC UA response delay or timeout. Sufficient time should be reserved for system services when designing tasks.
Online editing: When the OPC UA server is running, it is allowed to add network publishing variables through online editing without restarting the server. The newly added variables will be dynamically added to the address space.
- ABB
- General Electric
- EMERSON
- Honeywell
- HIMA
- ALSTOM
- Rolls-Royce
- MOTOROLA
- Rockwell
- Siemens
- Woodward
- YOKOGAWA
- FOXBORO
- KOLLMORGEN
- MOOG
- KB
- YAMAHA
- BENDER
- TEKTRONIX
- Westinghouse
- AMAT
- AB
- XYCOM
- Yaskawa
- B&R
- Schneider
- Kongsberg
- NI
- WATLOW
- ProSoft
- SEW
- ADVANCED
- Reliance
- TRICONEX
- METSO
- MAN
- Advantest
- STUDER
- KONGSBERG
- DANAHER MOTION
- Bently
- Galil
- EATON
- MOLEX
- DEIF
- B&W
- ZYGO
- Aerotech
- DANFOSS
- Beijer
- Moxa
- Rexroth
- Johnson
- WAGO
- TOSHIBA
- BMCM
- SMC
- HITACHI
- HIRSCHMANN
- Application field
- XP POWER
- CTI
- TRICON
- STOBER
- Thinklogical
- Horner Automation
- Meggitt
- Fanuc
- Baldor
- SHINKAWA
- Other Brands
- UniOP
- KUKA
- Iba





































































































































